Testimony of Danielle Brian, POGO's Executive Director on Inadequate Security at the Department of Energy Nuclear Weapons Complex before the House Government Reform Subcommittee on National Security, Emerging Threats and International Relations
Mr. Chairman, I commend you for holding these important hearings. The Project On Government Oversight (POGO) is an investigative organization that works with inside sources to improve public policy. Founded in 1981, POGO is a politically-independent, nonprofit watchdog that strives to promote a government that is accountable to the citizenry.
In early 2001, POGO began its investigation into nuclear security at the Department Of Energy (DOE) after more than a dozen high-level departmental security experts came forward with concerns regarding inadequate security at the DOE's nuclear weapons facilities. Just prior to September 11, 2001, POGO completed that investigation, concluding that the nation's ten nuclear weapons facilities, which house nearly 1,000 tons of weapons-grade plutonium and highly-enriched uranium, and the transportation system for weapons and nuclear materials regularly fail to protect this material during mock terrorist attacks. The results of that investigation were issued in the POGO report, "U. S. Nuclear Weapons Complex: Security at Risk." Even though it is now two years old, I daresay the problems identified are still relevant today. I ask that it be included in the record.
We briefed the NSC on multiple occasions, Homeland Security, various Pentagon groups including the Scowcroft End-to-End Review team, the Nuclear Command and Control staff, the White House OMB, among others, on our findings. We were encouraged when we met with officials of Homeland Security, who had seemed to understand the problems at DOE. They were particularly aware of problems with DOE oversight of the facilities, specifically personnel who continue to defend the status quo. In fact after our briefing to Homeland Security, I expected them to look at me with disbelief. Instead, however, a detailee from the Pentagon said, "You realize we are more concerned about the lack of security at DOE facilities than you are." They advised that they were establishing red teams to independently test security at DOE facilities in the April 2002 time frame. However, it never happened.
There are ten major DOE sites that have weapons quantities of plutonium and highly-enriched uranium, many of which are located near metropolitan areas including the San Francisco Bay area, Denver, Albuquerque and Knoxville. In order to perform their missions, a number of these sites do not need any Special Nuclear Material, and others certainly don't require the quantities that are currently being stored at the sites, but bureaucratic fiefdoms protect the status quo. There are three major threats to these facilities:
- theft of plutonium or highly-enriched uranium to create a crude nuclear weapon;
- terrorists gaining access to plutonium and highly-enriched uranium and using conventional explosives to create radiological sabotage, or a dirty bomb; and
- terrorists gaining access to plutonium and highly-enriched uranium and creating an Improvised Nuclear Device (IND) - a sizable nuclear detonation within minutes.
Weapons grade material stolen from a DOE facility could be used by a terrorist group to either fabricate a crude nuclear weapon or create a "dirty bomb." This is not as far-fetched as some might believe. In fact, in full-scope mock terrorist attack tests performed by the government at DOE facilities, half the time mock terrorists are successful in breaking in, stealing significant quantities of Special Nuclear Material and leaving the site.
Theft, however, requires that the terrorists get into a facility and back out with the material. What we have found in our investigations is that a suicidal terrorist would not have to work that hard. Instead, a successful suicidal terrorist attack at several of our DOE weapons facilities could result in a sizeable nuclear detonation at the facility itself. A terrorist group does not have to steal nuclear material, create a nuclear device, transport it to the United States, and detonate it in a major city. They could simply gain access to the material at a U.S. nuclear facility - some of which are near large metropolitan areas - and tests have shown they could accomplish the same outcome. This type of homemade bomb is called an Improvised Nuclear Device, or IND. Such a detonation can be created by using conventional explosives brought into the facility in a backpack and combined with particular kinds of Special Nuclear Materials stored at these sites.
For example, in October 2000, there was a mock attack test of the security at Technical Area-18, a facility at Los Alamos National Laboratory that contains many tons of Special Nuclear Material. The mock terrorists successfully entered a facility and the guard force could not get them out. The mock terrorists had enough time to have been able to create a sizeable nuclear detonation. The Senate Foreign Relations Committee held important hearings on this threat in March of 2003. In fact, in a recent CIA pamphlet summarizing typical Chemical Biological Radiological and Nuclear devices of interest to al-Qaida and other terrorist groups, they highlighted both dirty bombs and Improvised Nuclear Devices as two of their greatest concerns.
Improvised Nuclear Devices pose a great concern at a number of DOE facilities. In the mid-90s, the DOE made this vulnerability a highly-classified "Special Access Program"(SAP), and as a result no one could even talk about it unless you were one of the select few with a "need to know" - even though the problem is simple physics. Many inside DOE believe it was "SAPPED" because they didn't want to spend the money to address the vulnerability. A few months after a discussion of this vulnerability in the POGO report based on unclassified sources, General John Gordon, then-National Nuclear Security Administration (NNSA )Administrator, ordered a major change in security strategy to address the Improvised Nuclear Device vulnerability. Until that time, the strategy at most sites with Improvised Nuclear Device vulnerabilities was to "contain" the terrorists in the facility, and not let them out. Guards now are supposed to "deny" terrorist access to the facilities, because if the terrorists do get access to certain kinds of material, they can create an Improvised Nuclear Device in minutes. This is a very important step, if DOE can actually implement it.
We believe the single most important element to improve security at the nuclear weapons facilities is a realistic Design Basis Threat (DBT). The DBT is the threat that these facilities are required to defend against - the number of outside attackers with the help of active and passive insiders. It also includes the kinds of weapons likely to be used by potential adversaries. In May 2003, 20 months after 9/11, DOE finally substantially increased the DBT at Level 1 sites - sites with full-up nuclear weapons, test devices and partially dismantled or assembled weapons. DOE deserves credit for this important step, unfortunately the upgrades will not be fully implemented until 2009 - eight years after 9/11.
The other nuclear weapons sites, however, still have a long way to go and the new DBT for them is wholly inadequate. POGO has learned from Special Operations personnel and others in the Pentagon that al-Qaida would be expected to attack one of these facilities with a squad sized unit - The Army Special Forces size a squad at 12, and the Navy SEALS size a squad at 14 attackers. The way we understand it, even under the new DBT for Level 2 facilities - which contain large quantities of weapons grade plutonium and uranium with Improvised Nuclear Device vulnerabilities - DOE will only be protecting against far fewer attackers. Currently, DOE is determining its security requirements based on how much money it is willing to spend on security. This is backwards. Instead, DOE should determine the realistic threat, then require the facilities to size the protective strategy to meet that threat. Hopefully the Committee can encourage DOE to determine its security needs based on the intelligence community's Postulated Threat in your closed session.
We keep seeing evidence of security failures even without an attack on these facilities. All three of the weapons labs have had serious management and security problems in just the last few months. Top security officials at both Los Alamos and Livermore have been replaced. Only six months ago, a management scandal broke, involving some security issues including over 300 stolen or missing computers that the IG testified before Congress may have contained classified information. Now we have missing plutonium. At Livermore a set of keys and a security card to access sensitive areas were missing for weeks without being reported. In addition, members of the Livermore SWAT team claim they could not defend the lab in the event of a terrorist attack. At Sandia, there has also been a series of security lapses including guards sleeping and keys missing that are being investigated by Senator Grassley. Clearly security still takes a back seat at these facilities.
The scattering of special nuclear materials across the country is a leftover from the Cold War, when there were many more missions for the various sites. Now, a number of sites have virtually no national security mission, however, they continue to store and try to protect tons of nuclear materials at great cost. Currently, DOE cannot adequately protect this material, and security at each site unnecessarily increases redundancies and costs. However, DOE has resisted many consolidation opportunities as it would threaten fiefdoms and potentially even lead to (gasp) the closing down of facilities.
In addition to requiring a DBT that will address Improvised Nuclear Device vulnerabilities, POGO makes the following recommendations:
CONSOLIDATION OF NUCLEAR MATERIALS
The Base Realignment and Closure Commission should be empowered to recommend closing the unneeded and redundant DOE sites, as well as those sites that have no national defense mission. Not only do the unnecessary sites cost the taxpayers billions annually, but also present a significant health and safety risk to the nearby communities.
Another solution to this problem would be to consolidate nuclear materials to fewer, more easily-protected, sites. Not only would this save money, it would reduce the risk to the public. A plan by the DOE to consolidate nuclear materials at Savannah River and Oak Ridge at underground facilities should have been operational by now, but has been derailed by the bureaucracy. On May 28, 2003 Undersecretary Robert Card, in a Memorandum to the Program Offices, advised that,
"The first question for a site to consider is 'is there a way to reduce the targets by consolidating material, documents, vaults, and access areas or even better, exporting material or documents to other more permanent or hardened sites?' Target reduction is preferred to adding personnel or technology to protect current targets, and it better responds to the possibility of further DBT increases."
This is certainly commendable language, however, these same directions have been issued to the field for twenty years with little or no impact. In recent years, there has been some marginal consolidation within sites. Some small DOE sites with little or no Special Nuclear Materials have been shut down. Rocky Flats is the only site with significant quantities of plutonium that is in the process of being de-inventoried. However, there has been no effort to move this material to underground sites which can be more economically and effectively protected.
A case in point is TA-18 at Los Alamos. In 2000, then-Energy Secretary Bill Richardson directed that this site, which is at the bottom of a canyon and cannot be protected, be deinventoried of its Special Nuclear Materials by 2003. These materials and the mission were to be moved underground to a currently empty and hardened underground facility at the Nevada Test Site. Here we are, and not one gram has moved in that direction. Last year, NNSA Deputy Administrator Everet Beckner ordered then-Lab Director John Browne to expedite the deinventorying. New excuses are emanating from Los Alamos that they still aren't ready, but will begin moving the materials in 2006. I believe they are betting on turnover at DOE Headquarters, and the inattention of the Congress.
MAKE TESTS MORE REALISTIC
According to experts interviewed by POGO, including former and current members of Special Forces units used to test security at sensitive facilities, and current and former DOE and DOD officials, the tests of security at the weapons facilities are still seriously dumbed-down - often to the point of absurdity. For example, just recently during a mock theft scenario, "terrorists" were not allowed to go out the same hole in the fence they came in, requiring them to run all the way around the fence line to leave the facility. If they had been allowed to use the hole, they would have been able to leave the facility without even having engaged any of the protective forces. In another recent example, the mock terrorists were required to stay on the road in order to leave the facility. DOE should use trained adversary forces, for example the Special Forces unit out of Fort Bragg, or the Navy SEALs to perform these tests. These teams are trained to think and act like terrorists. Instead, typically protective forces from other sites are used as mock terrorists - yet they lack this very specialized training. In addition, advanced warning is given to the sites - often months in advance - that a test is scheduled, and the tests follow scripts of what the "terrorists" can and can't do. The three advantages a terrorist has are surprise, speed and violence of action - elements that are not factors in these dumbed-down tests - yet the mock terrorists still accomplish their "mission" all too often.
IMMOBILIZE EXCESS PLUTONIUM
Over 50 tons of our plutonium have already been declared excess and could be immobilized - glassified and surrounded with a radiation shield so that it would be less attractive for theft. Instead of moving ahead with this plan, however, the U.S. has decided to bet on an unproven technology of turning this excess plutonium into reactor fuel called MOX, which will still result in the creation of more plutonium. We believe this is a mistake. Until the excess plutonium is permanently immobilized, it will continue to pose an unnecessary homeland security vulnerability.
MOVE SECURITY OVERSIGHT OUT OF DOE
The Congressionally-created National Nuclear Security Administration (NNSA) exacerbated the problem by elevating the same people who have managed this debacle over the last three decades, and the culture has not changed. All the way up the chain of command, from the contractor self-assessments, the Area Offices, Operations Offices have been found by the IG and GAO to have been all too willing to sugar-coat, and sometimes even falsify their security reports.
One way to counter this culture is to improve oversight of security, and move the Independent Oversight Office out of DOE. Oversight of nuclear security should be more independent from those charged with implementing security by making the DOE Office of Independent Oversight an Independent Nuclear Facilities Security Board that is separate from DOE. A model would be the Defense Nuclear Facilities Safety Board. This board would report directly to the Congress and be empowered to assess security in the nuclear complex.
Another option would be to make security oversight of DOE facilities a DOD responsibility, perhaps under the Nuclear Command and Control Staff. Given that the materials stored at DOE facilities are often equally attractive to terrorists as those stored at DOD sites, and DOD is the "customer" for DOE made weapons, it is perfectly appropriate to have our most highly trained security specialists responsible for this job.
INCREASE SECURITY FUNDING, BUT SPEND RESOURCES MORE EFFICIENTLY
The United States spends over $1 billion annually on security at DOE sites. We are not getting our money's worth. We are spreading our resources inefficiently by protecting sites we should not have to protect either because Special Nuclear Materials are not needed there, or it is not needed there in massive quantities. Clearly the new DBT will require more money, but money should not be thrown at the problem without evidence that a real plan to implement security upgrades efficiently is in place. The first step is to consolidate and store the materials underground. In the past, DOE security has hit obstacles obtaining increased budgets from within the department, from OMB and from the Congress in large part because they have simply lied about the status of security. For example in early 2002, then-NNSA Administrator Gordon wrote a letter to the Washington Post denying POGO's findings, and assuring the public that security was adequate at the nuclear sites. One month later, DOE was talking out of the other side of its mouth begging OMB and the Congress for a half-billion dollar increase in funding because of dire security problems.
MORE CONGRESSIONAL OVERSIGHT
There are two things that move any bureaucracy: one is sustained press attention to a problem and second is congressional oversight. Over the last 20-30 years, there has never been sustained press attention paid to security debacles at DOE because the Department has been able to hide behind overclassification.
According to the President's Foreign Intelligence Advisory Board, "The panel has found that DOE and the weapons laboratories have a deeply rooted culture of low regard for and, at times, hostility to security issues, which has continually frustrated the efforts of its internal and external critics, notably the GAO and House Energy and Commerce Committee." POGO compiled a list of over 50 reports, hearings, testimony, Commissions detailing DOE security failures - not including the more recent IG and GAO findings.
The Congressional hearings spurred by the Los Alamos cyber security breaches focused on two specific incidents of security failures, Wen Ho Lee and the missing hard drives, but did not deal with the systemic physical and cyber security problems at the nuclear weapons complex. Incidentally, no significant security improvements have been implemented as a result of these high profile cases. Without sustained and intensive scrutiny and oversight, DOE briefings and testimony will not reveal the actual status of security. It is ultimately up to Congress to keep at this. I believe it is some of the most important work you can do.
Here's a suggestion for a next step: In mid-2002 the Scowcroft Commission finally issued their "End-to-End" review of security at DOD and DOE nuclear weapons facilities. We were advised that drafts of that report were very critical of DOE security and oversight. Despite Rep. Markey's request to see a declassified version of the report, it was never released. Apparently the GAO never saw the drafts or the final version of that report either. We encourage the Committee to obtain a copy of the drafts of the report and interview the authors.
Thank you very much for commissioning this GAO report and inviting me to testify.
Related Content

New Appointee to Lead Intelligence Department Is a Threat to Our Security
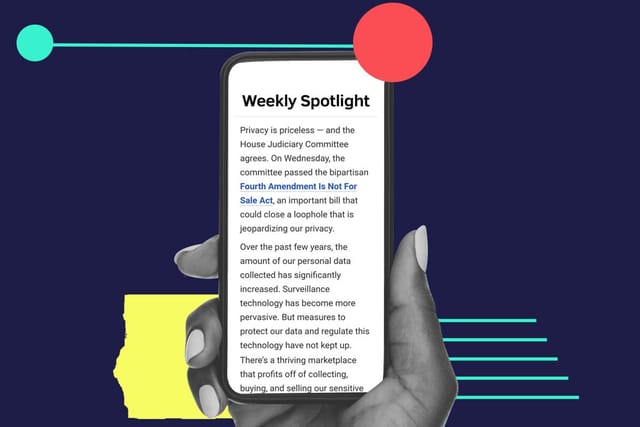
Lawmakers need to close the data broker loophole to prevent unaccountable, inexperienced government officials from targeting Americans